Author:
(1) Yigit Ege Bayiz, Electrical and Computer Engineering The University of Texas at Austin Austin, Texas, USA (Email: egebayiz@utexas.edu);
(2) Ufuk Topcu, Aerospace Engineering and Engineering Mechanics The University of Texas at Austin Austin, Texas, USA (Email: utopcu@utexas.edu).
Table of Links
Deterministic Baseline Policies
Temporally Equidistant Prebunking
VI. TEMPORALLY EQUIDISTANT PREBUNKING
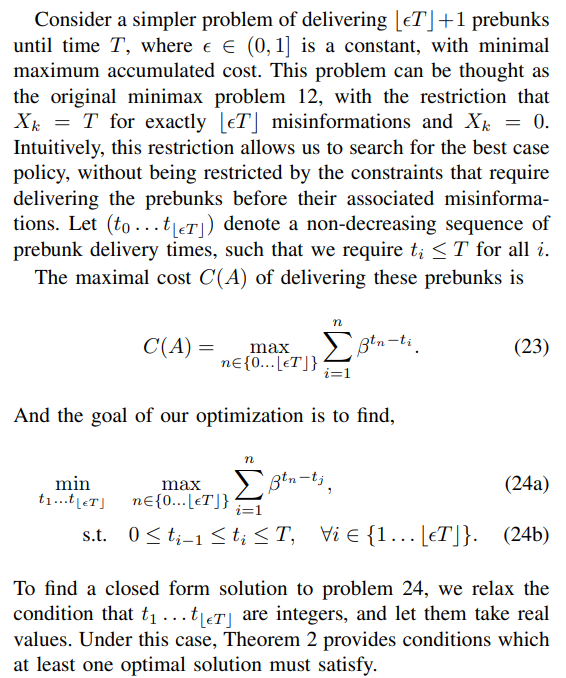
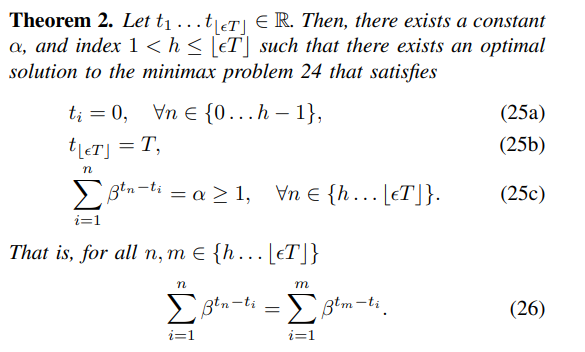
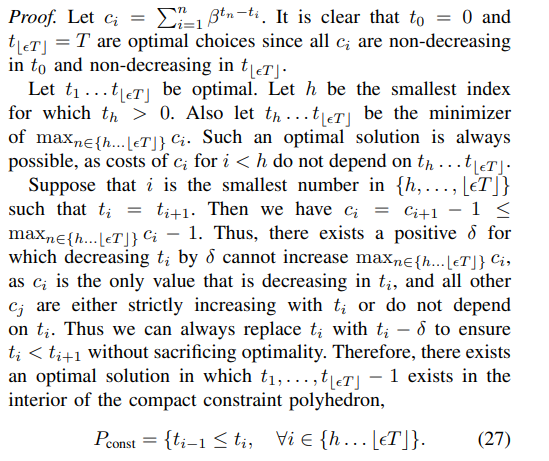
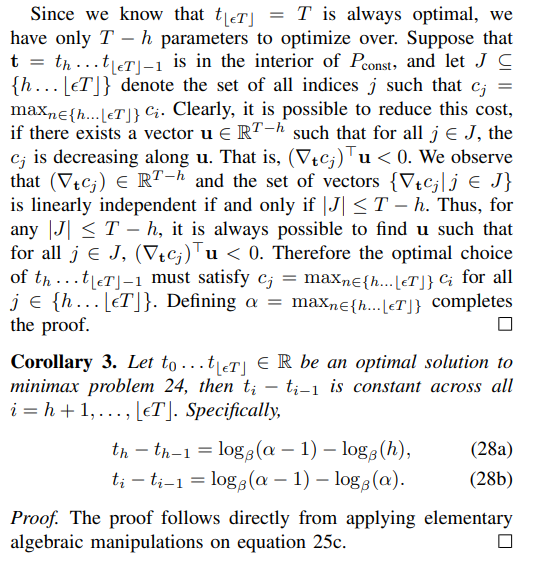
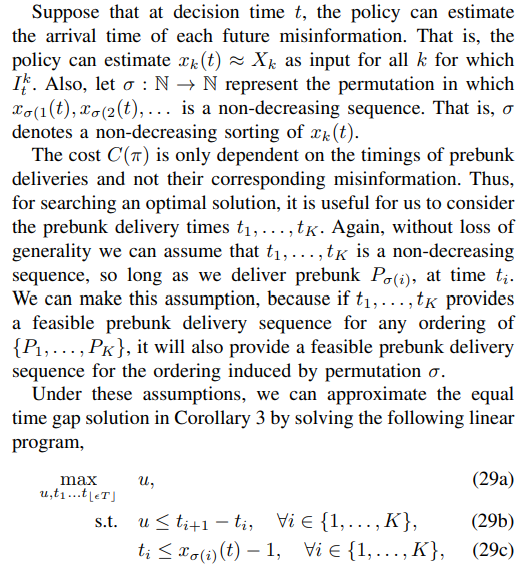
Thus, by Corollary 3, the optimal policy delivers prebunks evenly across all time steps with equal time gaps in-between. Intuitively, this means that the optimal policy tries to maximize the time gap between each consecutive prebunk delivery. We emphasize that Corollary 3 only holds exactly when we have the restricted problem 24, without the additional constraints.
We can approximate this equal time gap policy in the general problem 12. The goal of the policy π in this case is to determine which Pk to issue at time t. Clearly, it is not optimal to provide a prebunk Pk to user c more than once, since doing so does not change the feasibility of problem and cannot reduce the maximal cost C(π). Thus, we can assume without loss of optimality that each Pk is in at most one At ∈ A. Hence, in its decision, the policy π only needs to take into account the misinformations Mk, for which it has not delivered any prebunk Pk yet. Without loss of generality, we assume that this set of misinformations is the finite set {M1, . . . , MK} as Assumption 2 guarantees that at each time t there are finitely many Mk for which Ik ̸= ∅.
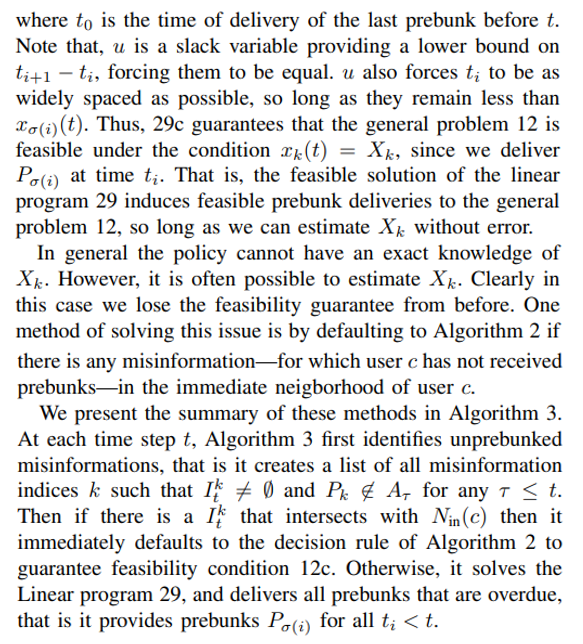
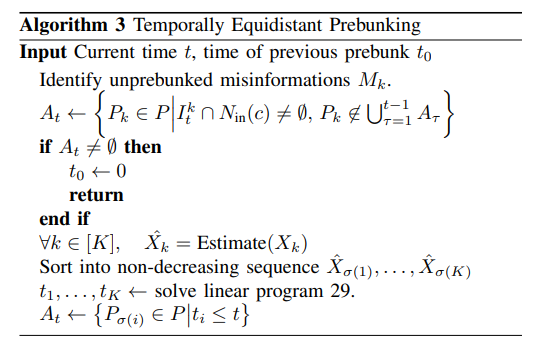
In our experiments, we use a Monte Carlo method and estimate Xk by simulating misinformation propagations in the local network Gc, and obtaining a frequentist estimation of how long it takes for the misinformation to reach from any node in the network to the central user c. Clearly, this estimation method does not scale to large networks. However, in our tests, for small choices of m the local network around user c remains small enough to permit this approach. It is possible that there are other estimation methods that admit more accurate estimations or scale better to large networks, which might provide better results.
This paper is available on arxiv under CC 4.0 license.

